Stolen trailer from downtown Joplin; Do you recognize these men or vehicle? Join the Community Action Group, Joplin Area Stolen Items | KSNF/KODE | FourStatesHomepage.com

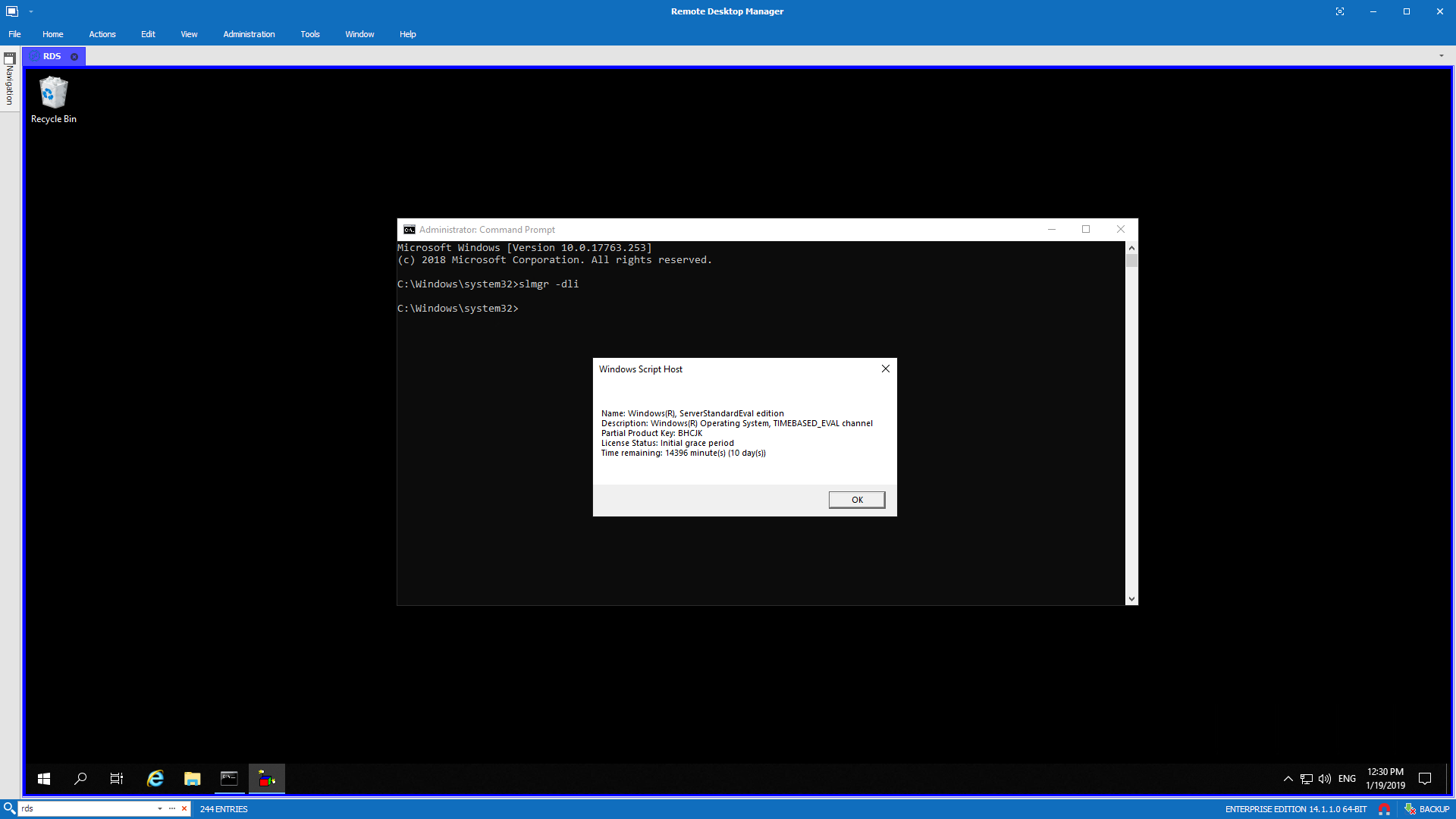
Microsoft Warns of Rise in Stolen Cloud Tokens Used to Bypass MFA | Data Center Knowledge | News and analysis for the data center industry

Pre-RFC: Remove Rust's dependency on Visual Studio in 4 (...complex?) steps - compiler - Rust Internals